Some Inventive fraudsters are modifying phony POS terminals to hold the credentials of actual merchants. Then they conduct fraudulent return transactions to load reward cards or debit cards, then cash out the stolen cash at ATMs.Throughout the post, We've emphasised the importance of cybersecurity and the need to prioritize the safety of personal e
 Neve Campbell Then & Now!
Neve Campbell Then & Now! Jennifer Love Hewitt Then & Now!
Jennifer Love Hewitt Then & Now! Monica Lewinsky Then & Now!
Monica Lewinsky Then & Now! Samantha Fox Then & Now!
Samantha Fox Then & Now!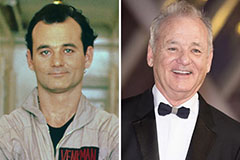 Bill Murray Then & Now!
Bill Murray Then & Now!